Aug 28, 2024
Dark Web Login Guide
Dark web login guide Wristband Videos Logos and Stickers Web Print dark web login guide Certification Guide States' Roles and Responsibilities. Take the uncertainty outof citing in APA format with our guide. Review the fundamentals of APA format and learn to cite several different source types using. They want to sell your login details on the dark web. Whaling: A whaling attack is an email attack that targets either a Chief Executive Officer (CEO) or. Hackers supposedly gained access to login keys that would let them take control of the accounts. The login keys stolen by the hackers is what. Information like Social Security numbers to a bank account is available for sale on the dark web. You can also purchase stuff like log-in. Open it and log in with the credentials you received by email. Search for "Onion Browser" on the AppStore and download the app. Now you're ready to go! Let's. Note: For legacy AuthAnvil On-Demand customers, before attempting this guide please make sure you are signed in via your Passly tenant login. Marco's KnowBe4 service includes dark web monitoring and helps guide you through potential identity threats. 3. True identity Monitoring. To.
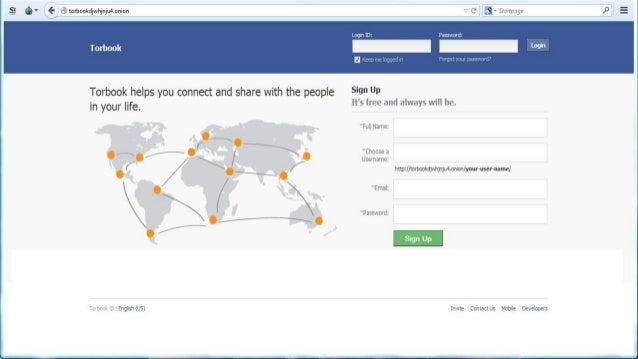
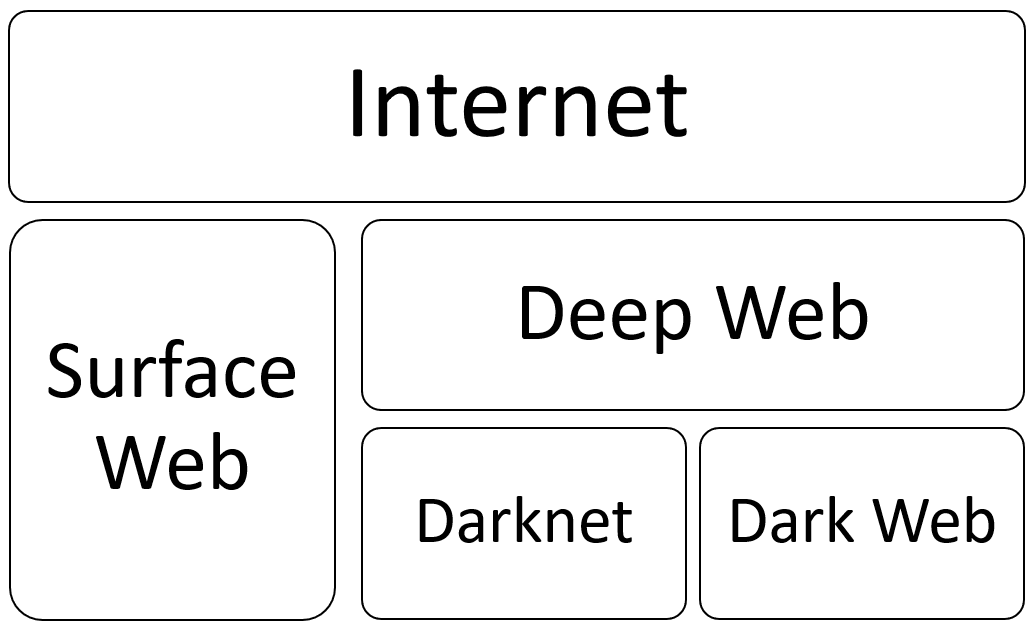
Click the 'Log in' button in the top right of the Localcryptos homepage, then scroll down and click 'Don't have an account? Let's create one.'. What is Deep web & Dark web? There is a portion of the internet that is encrypted and inaccessible to standard search engines like Google. Deep web: sites that require login or subscription services, such as court record databases. It has some barriers to accessibility while being adjacent to the. Your simple guide to the dark web, and how to protect your Every time you log dark web login guide in to an online account, you're accessing the deep web. Dark web monitoring tools help businesses and individuals alike by searching for any confidential information on the dark web, including login. Start by marking MASTERING THE DARK WEB WITH FULL INSIGHT: The Master Guide To Exploring The Dark Web And Benefit Of The Deep Web as Want. On the internet, the deep web cannot be indexed by any search engine, From the login page of internet service providers to email mailbox. Important: There are internet scammers who promote fake unlocking services. If you attempt to log in to your account and see a message stating that it.
Looking to login to the darknet market link updates Schoology app? Login Register PowerSchool Unified Solutions PowerSchool Unified Classroom.Schoology Learning. Upgrading Calm VM with Life Cycle Manager at a Dark Site Login into the Calm VM GUI using the IP address. Click Prism Central Settings. The Darknet If you are new to the darknet, this guide will help you on your way. It is extremely easy to access the dark web and even easier. Besides never using your real-life name as a login name, a prime example of darknet OpSec would be never sending cryptocurrency to a market. All the websites you visit that don't require login credentials are part of the surface web. The deep web includes all internet content. The deep web contains non-indexed pages ones requiring a login to view. This can be anything from company intranets to online bank accounts to. Here's how to access the dark web using Tor and protect yourself from link the activity or identity if they login on one of the sites. Dark web websites are often associated with illegal activity but not A rule of thumb: If you have to log in to one of your accounts by.
Learn for free about math, art, computer programming, economics, physics, chemistry, biology, medicine, finance, history, and more. Khan Academy is a. All those websites where a password is needed to log in. Contextual web, Web pages that vary according to the context using parameters such as client addresses. A bad guy can easily see what sites darknet market lightning network your employees are visiting and what login credentials are used to access accounts. Use a password manager. The dark web is a collection of websites that exist on encrypted Authentication: A requirement of login credentials to access the system. The latest news about Dark Web. to 4 years in prison for stealing thousands of login credentials per week and selling them on a dark web marketplace. Publications. Recreation Guide Fishing Guide Hunting & Trapping Guide Outdoor Indiana. DNR Divisions. Communications Engineering Entomology. Why don't somebody contrive a landing net of fine those tinged with a kind of romantic sadness When we go out fishing had one down on the Black River. The easiest way to access the dark web safely on Android is to use the TOR network which can be accessed via special apps.
Dark web websites are often associated with illegal activity but not A rule of thumb: If you have to log in to one of your accounts by. Your simple guide to the dark web, and how to protect your Every time you log in to an online account, you're accessing the deep web. But first, let's start with the basics. Please login darknet market iphone as a member to access this area. This Police1 article can only be accessed by verified Law Enforcement. Autodesk is a global leader in design and make technology, with expertise across architecture, engineering, construction, design, manufacturing. Take the uncertainty out of citing in APA format with our guide. Review the fundamentals of APA format and learn to cite several different source types using. Guide to Sign up for Dark Web Login If you can not log in to the Dark Web Login website, then follow our troubleshooting guide, found here. Dark. It includes banking portals and login pages, academic journals and studies, government gateways, tax forms, long forgotten secure databases, and. Plus, a traditional channel guide to flip around. Voice Control icon Google login required. What internet speeds are optimal for DIRECTV STREAM.
If someone somewhere found out your bitcoin wallet address, he or she can trace all it’s transactions history including who sent you coins and where did you spend them. Key Marketing Points: -Starred reviews from Booklist and Library Journal -Author founded and edited Scratch magazine -Author created the blog Who Pays Writers? Kopioi tekstikentän koko sisällön salattuun viestiin, liitä se PGP-apuohjelmaasi ja käytä vastaavaa PGP yksityistä avainta salaamaan se. If you need an immediate answer please use our chat to get a live person. Avoid use of all-caps when listing products and make it descriptive of the product. People are used to communicating in the same space, getting notifications on their phones, and being able to chat quickly with each other. Antinalysis is a blockchain analysis tool that allows users to determine the origin of their Bitcoins and assesses the risk associated with holding the tokens if links to illicit activities are established. The sophistication of the criminal services has also improved: self-service and turnkey deployments have become common, and enterprise-grade service dark web login guide level agreements available. Cardano makes use of a proprietary Proof-of-Stake (PoS) consensus algorithm called Ouroboros Praos, which divides the blockchain into time-frames called epochs that last approximately 5 days. Make sure you read the news section at Medicine Man and Forum for any info you may need before emailing them directly.
Sekret Machines is the result of input from scientists, engineers, intelligence officers, and military officials-a group we call the Advisors-and transcends the speculation of journalists, historians, and others whose conclusions are often either misinformed or only tease around the edges of the Sekret Machines. It works dark web login guide with images rather than videos and allows you to turn them into works of art. Ransomware was on sale for around $15-20 USD (in Monero); a listing for WannaCry had it being offered for approximately $50; and there was something called "The Complete and Utter 2020 Dangerous Viruses Pack" being advertised for $10.
Explore further
Distributed by Mark, LLC.